7 Tips Founders Need To Know About Securing Their Startups
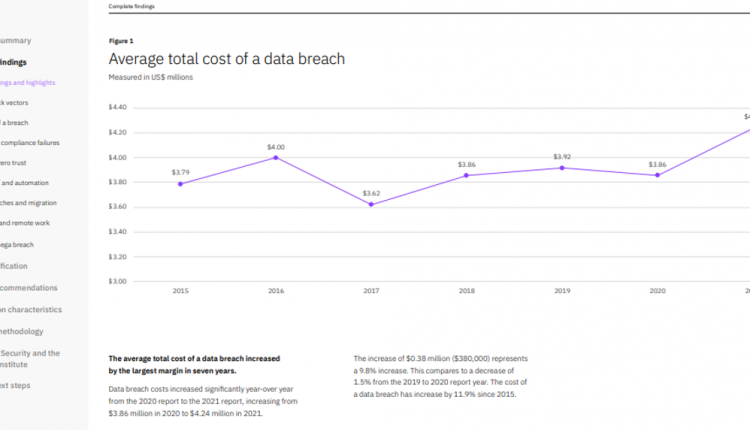
If you have been keen on the news headlines, you might have noticed the increase in cybersecurity threats, especially in the most recent days. Hacking has become one of the biggest problems of the modern age. Data breaches, malware infections, data hijacking, phishing attacks, DDoS attacks, and many more have infiltrated the technology world, leaving victims with dire reputational damages, money losses, business closures, among many other consequences. Details of IBM’s 2021 Cost of Data Breach Report now show that the global average cost of a data breach stands at $4.24 Million. See more information on this report in the graph below.
Small, medium, and big businesses alike are not spared from the double-edged sword of hackers. In the past, there has been the notion that “my startup is too small to be targeted.” However, reports now indicate that small businesses are a lucrative spot for hackers. A recent report showed that 43% of data breaches targeted small to medium-sized businesses. This is a considerable chunk, meaning that founders and small business owners should install adequate mechanisms to defend their cybersecurity walls. This brings us to today’s primary agenda: The measures founders must put in place to stop cybersecurity threats.
You are struggling to build a secure network in your company. You need to hire a lot of people with cybersecurity knowledge, but they are expensive.
Use AlvaComm for structured cabling system for cybersecurity, to make it easy for you to build a secure network in your company!
Securing Your Startup
One of the reasons small and medium-sized businesses tend to be extra-vulnerable to hackers is that most owners do not know how to secure them. Moreover, most of these businesses do not have the resource muscles to secure their walls, such as those possessed by established companies. Again, most founders will leave their ventures open to attacks because they see their businesses as of no value to hackers. But that is actually not the case. What might seem valueless to you might be of great importance to a hacker. As such, you must ensure that you protect your business at all costs. You do not have to spend resources worth millions to do that. Here are some of the top 7 low-cost tips founders can use to protect their ventures.
1: Conduct Regular Threat Assessments
Before you start investing in security tools such as firewalls and antimalware software, you will first need to assess the well-being of your security walls. Regular threats analysis shows a clear picture of the potential threats, weaknesses, and vulnerabilities spots in your defense system and the effectiveness of your defense mechanisms to handle these threats. Once the threat analysis is completed, you will know how and where to prioritize your resources.
2: Data Encryption Using SSL Certificate
Having a business website brings lots of low-hanging fruits to the business. However, a website could also be the most vulnerable element of your business if adequate measures are not taken to secure it. Using a man-in-the-middle attacks hacking technique, hacks can easily sniff and eavesdrop through communication between you and your users. However, it would be almost impossible for a hacker to decipher encrypted data. HTTPS is the standard security protocol that encrypts data. Encrypted data is transferred in a special kind of form referred to as a ciphertext instead of plain text. SSL certificate is the technology behind the working of an SSL certificate.
Any serious business owner who values the security of their website and users’ information must buy an SSL certificate. To do so, first assess the site’s structure and decide the type of SSL security that you can install on the server. As there are a few famous but low-priced SSL certificates like rapidssl cert, cheap Thawte SSL123, GlobalSign SSL cert, etc. The reason is that the certificate will secure all users’ sensitive data by concealing it from unintended parties.
3: Prioritize Physical Security of Your Network and Business As A Whole
It is so essential to secure your company from a software perspective. But it is even more important to prioritize physical security as well. The logic here is that physical breaches could be even more devastating than a virus attack. Imagine the scenario where you have invested a lot of resources in expensive firewalls and antimalware software, only for the hard drive carrying all data to be stolen. It would be a wasted investment. Therefore, as you invest in adequate security tools and software, never forget the weight that physical security carries.
4: Access Controls
Apart from limitation to premise accesses, it is also vital that you limit access to data centers and data processing systems. In the recent past, we have witnessed some of the most devastating insider attacks. It means that your employees could be the biggest enemy of your cybersecurity systems. Access controls are the mechanisms laid in place to mitigate the risks associated with unauthorized access to information centers. When implemented correctly, access controls can go a long way toward preventing all risks of data breaches that originate within the organization.
Opening up information assets for free access by any member of your organization could potentially cost you. The best practice will be limiting information access to only those members of your organization who have business with specific data. It is also here that the principle of the least privilege must apply. According to the principle, “a subject should be given only those privileges needed for it to complete its task.” So if an employee does not need specific data to accomplish a task, the employee should be limited from accessing such data.
5: Strict Password Policies That Apply To All Stakeholders
Most hackers tend to try accessing a network by breaking through the front door. They will try to crack the passwords in the hope that their passwords combinations will work and give them access to users’ accounts. Poor password practices make your business accounts vulnerable in the eyes of hackers. It should be alarming to learn that over 80% of all breaches are related to poor password practices.
The only remedy to this is to ensure that all stakeholders within your organization adhere to best password practices. For instance, you must have a clear password guideline requiring your employees to set their passwords to specific character lengths and combinations. The logic here is that hackers find long and complex passwords almost uncrackable. Secondly, employees should be informed of all the best password storage sources. You must note that writing down passwords or storing them in browsers can easily compromise business accounts. Other best practices include not reusing passwords for multiple accounts and frequently changing the passwords.
Apart from passwords, founders are advised to secure their startups by fortifying their login processes using two-factor authentication. It is a vital procedure because it protects your business accounts in the situation where the hackers successfully crack the passwords puzzle. The hacker will be denied access because they lack the extra authentication factor.
6: Have a Cybersecurity Training and Awareness Program
A cybersecurity training and awareness program can be pivotal in securing small and medium-sized businesses. Through the program, employees will be taught the various potential threats that could hit them. The best strategies the employees can employ to stay safe from such threats, and the right course of actions to take in case of a suspected breach. The training and awareness program can also help deal with insider threats as you stipulate the consequences of such attacks. It is recommended that you undertake the cybersecurity training and awareness program immediately after launching your business. This will help create a culture of cybersecurity from the start.
7: Frequently Update Your Software and Operating System
Before launching your business, you should ensure that you are running on the latest software and operating systems versions. The reason is that the latest versions are well-suited to deal with the loophole and vulnerabilities that existed in the previous versions. Updating your software frequently will highly bolster your security.
Read Next:
Conclusion
Startups are vulnerable to attacks. This article has spelled out some of the tips founders can use to safeguard Startup. It would be best to have these measures and many others working in unison. One or two measures can never be enough to safeguard your business. Additionally, you should remember that these tips do not give you full immunity to the hackers’ wraths. As such, you must always have a contingency plan. Backing up your data frequently could be of great essence if these measures fail.